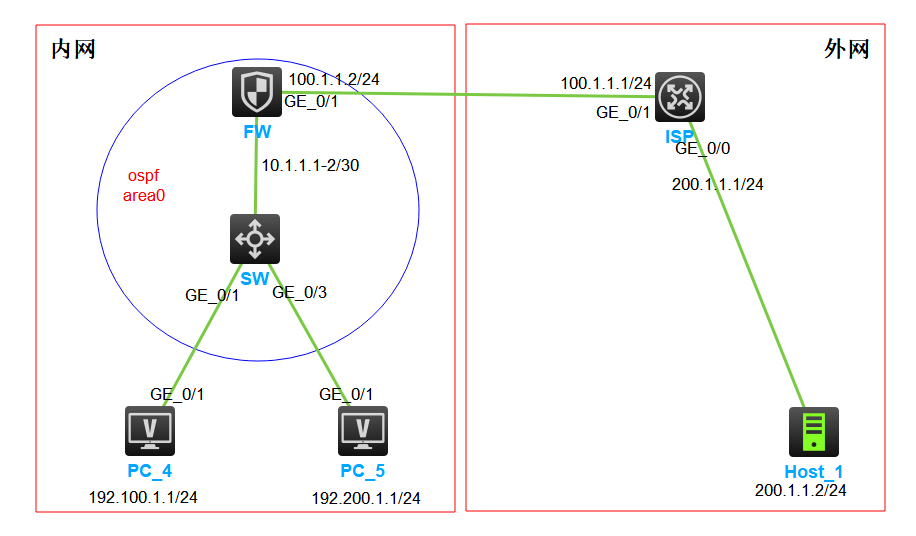
防火墙NAT Outbound+NAT server (基础 HCL实验)
实验须知:
1:掌握防火墙与其他设备运行OSPF ,开启安全策略;
2:掌握防火墙配置nat outbound配置 ,以及需要的安全策略;
3:nat server 配置以及 三条安全策略;
配置步骤
1、交换机SW配置;配置vlan ,配置IP地址,配置OSPF路由
[SW] vlan 10 //互联vlan [SW] vlan 100 //业务vlan PC-4 [SW] vlan 200 //业务vlan PC-5 [SW-vlan200]port g1/0/3 [SW-vlan100]port g1/0/1 [SW-vlan10] port g1/0/2 [SW-Vlan-interface10] ip address 10.1.1.2 30 //配置IP地址 [SW-Vlan-interface100]ip address 192.100.1.254 24 [SW-Vlan-interface200]ip address 192.200.1.254 24 [SW]ospf //配置OSPF 划分区域 发布路由信息 [SW-ospf-1]a 0 [SW-ospf-1-area-0.0.0.0]network 10.1.1.0 0.0.0.3 [SW-ospf-1-area-0.0.0.0]network 192.100.1.0 0.0.0.255 [SW-ospf-1-area-0.0.0.0]network 192.200.1.0 0.0.0.255
2、防火墙FW配置:接口配置IP 划分区域,配置OSPF协议
Press ENTER to get started. Login: admin Password admin //默认密码 [H3C]sysname FW [FW][FW]security-zone name Trust [FW-security-zone-Trust] [FW-security-zone-Trust]import interface g1/0/2 //接口加入安全域 [FW]security-zone name Untrust [FW-security-zone-Untrust]import interface g1/0/1 [FW-GigabitEthernet1/0/1] ip address 100.1.1.2 24 //接口配置IP 地址; [FW-GigabitEthernet1/0/2] ip address 10.1.1.1 30 [FW]ospf [FW-ospf-1] a 0 [FW-ospf-1-area-0.0.0.0]network 10.1.1.1 0.0.0.3 [FW-ospf-1]default-route-advertise always //向邻居通告一条默认路由,告诉邻居去往外面交给我
3、防火墙FW配置nat (实验为easy-ip方式)
[FW]acl basic 2000 //定义哪些数据流可以被NAT转换 [FW-acl-ipv4-basic-2000]rule permit source 192.100.1.0 0.0.0.255 [FW-acl-ipv4-basic-2000]rule permit source 192.200.1.0 0.0.0.255 [FW-GigabitEthernet1/0/1]nat outbound 2000 //接口上配置NAT,经过接口满足条件的数据流可以转换 [FW]ip route-static 0.0.0.0 0 100.1.1.1 //去往外面的路由都交给ISP转发
4、OSPF建立邻居策略(本实验就没有写具体的source IP 和destination IP)
[FW-security-policy-ip]rule 3 name l-t //本地local到trust区域(交换机连接的区域) [FW-security-policy-ip-3-l-d]source-zone local [FW-security-policy-ip-3-l-d]destination-zone trust [FW-security-policy-ip-3-l-d]service ospf //允许OSPF协议报文通过 [FW-security-policy-ip-3-l-d]action pass [FW-security-policy-ip]rule 2 name t-l //trust区域到本地local [FW-security-policy-ip-2-t-l]service ospf [FW-security-policy-ip-2-t-l]source-zone trust [FW-security-policy-ip-2-t-l]destination-zone local [FW-security-policy-ip-2-t-l]act pass [FW] dis ospf peer //要放行策略后,才能建立邻居关系 OSPF Process 1 with Router ID 100.1.1.2 Neighbor Brief Information Area: 0.0.0.0 Router ID Address Pri Dead-Time State Interface 192.200.1.254 10.1.1.2 1 36 Full/DR GE1/0/2
5、定义匹配NAT安全策略
[FW]security-policy ip [FW-security-policy-ip]rule 1 name t-u [FW-security-policy-ip-1-t-u]source-zone trust [FW-security-policy-ip-1-t-u]destination-zone untrust [FW-security-policy-ip-1-t-u]source-ip-subnet 192.100.1.0 24 [FW-security-policy-ip-1-t-u]source-ip-subnet 192.200.1.0 24 [FW-security-policy-ip-1-t-u]action pass
6:测试:在PC4 PC5访问公网100.1.1.1
<PC-4>ping 100.1.1.1 //在PC-4测试外网正常访问; Ping 100.1.1.1 (100.1.1.1): 56 data bytes, press CTRL_C to break 56 bytes from 100.1.1.1: icmp_seq=0 ttl=253 time=1.233 ms 56 bytes from 100.1.1.1: icmp_seq=1 ttl=253 time=1.113 ms 56 bytes from 100.1.1.1: icmp_seq=2 ttl=253 time=1.056 ms [FW]dis nat session //防火墙查看nat session会话表,可以看到 Slot 1: Initiator: Source IP/port: 192.100.1.1/184 Destination IP/port: 100.1.1.1/2048 DS-Lite tunnel peer: - VPN instance/VLAN ID/Inline ID: -/-/- Protocol: ICMP(1) Inbound interface: GigabitEthernet1/0/2 Source security zone: Trust
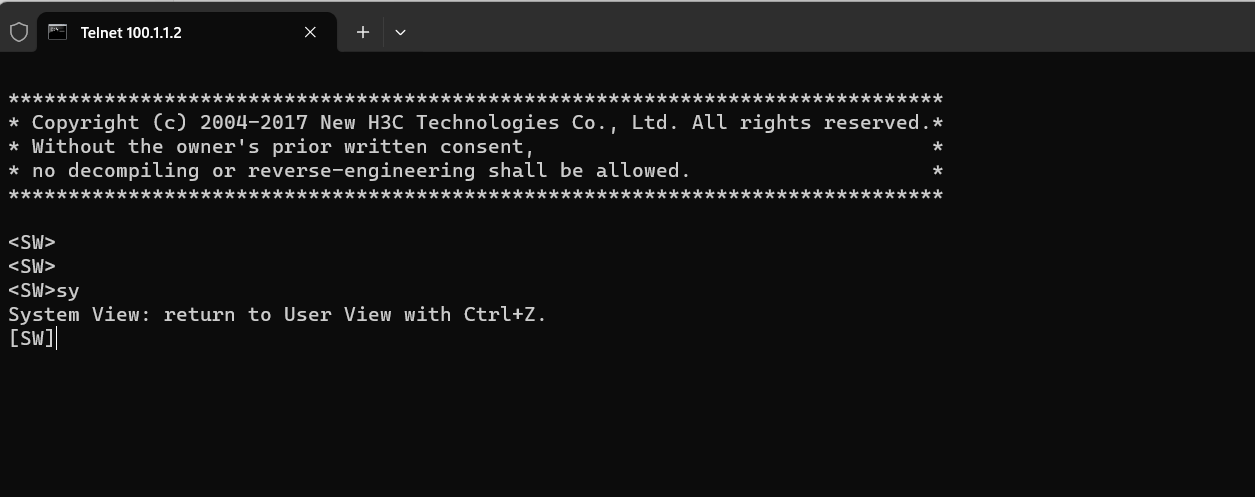
7、外网主动访问内网服务器(题目中用SW配置telnet 模拟服务器),在交换机SW配置telnet ;
[SW]telnet server enable [SW]line vty 0 63 [SW-line-vty0-63]authentication-mode none //为了方便实验效果,本题telnet 配置免认证 [SW-line-vty0-63]user-role network-admin
8、防火墙配置NAT server 功能 ,把telnet 服务主动提供外网访问,
[FW-GigabitEthernet1/0/1]nat server protocol tcp global 100.1.1.2 2233 inside 10.1.1.2 23 1: 需要知道提供外网访问功能是基于什么协议:比如tcp udp icmp 2: 可能会出现公网端口号被本身占用,所以需要注意,比如telnet 防火墙可能也会使用这个端口,建议修改,
9、配置nat server 需要的安全策略
[FW]object-group service 22 [FW-obj-grp-service-22]1 service tcp destination eq 2233 [FW-security-policy-ip]rule 6 name u-t //外到内的安全测率 [FW-security-policy-ip-6-u-t]source-zone untrust [FW-security-policy-ip-6-u-t]destination-zone trust [FW-security-policy-ip-6-u-t]service telnet [FW-security-policy-ip-6-u-t]act pass [FW-security-policy-ip]rule 4 name u-l //外到本地安全策略 [FW-security-policy-ip-4-u-l]source-zone untrust [FW-security-policy-ip-4-u-l]destination-zone local [FW-security-policy-ip-4-u-l]service 22 [FW-security-policy-ip]rule 5 name l-t //本地到内的安全策略 [FW-security-policy-ip-5-l-t]source-zone local [FW-security-policy-ip-5-l-t]destination-zone trust [FW-security-policy-ip-5-l-t]service 22 [FW-security-policy-ip-5-l-t]act pass
10、测试外网访问内网服务器;PC:Administrator>telnet 100.1.1.2 2233